In the rapidly evolving world of technology, securely connecting remote IoT (Internet of Things) devices has become a critical aspect of modern digital infrastructure. As businesses and individuals increasingly rely on IoT devices for automation, monitoring, and data collection, ensuring secure communication between these devices and cloud-based networks is paramount. In this article, we will explore how you can securely connect your Raspberry Pi to a remote IoT Virtual Private Cloud (VPC) without breaking the bank.
This guide will delve into the technical aspects of setting up a secure connection, including best practices, tools, and configurations that ensure your IoT devices remain protected from cyber threats. Whether you're a hobbyist, a small business owner, or an enterprise IT professional, this article will equip you with the knowledge and resources to implement a secure IoT VPC connection.
By the end of this article, you'll understand the importance of securing IoT devices, the role of Raspberry Pi in IoT deployments, and how to achieve a cost-effective solution for connecting remote devices to a VPC. Let's dive in and explore the possibilities of a secure IoT ecosystem.
Read also:Exploring Chicagos O Block A Comprehensive Guide To The Heart Of Illinois
Table of Contents
- Introduction to IoT VPC
- Raspberry Pi in IoT Deployments
- Why Secure Connections Are Critical
- Setting Up a VPC for IoT Devices
- Securing Remote IoT Connections
- Tools and Technologies for Secure IoT
- Best Practices for IoT Security
- Cost-Effective Solutions for IoT VPC
- Troubleshooting Common Issues
- Conclusion
Introduction to IoT VPC
IoT (Internet of Things) refers to the network of physical devices embedded with sensors, software, and connectivity, enabling them to collect and exchange data. A Virtual Private Cloud (VPC) is a private network within a cloud environment, allowing users to securely host and manage their resources. Combining IoT with VPC creates a robust infrastructure for managing IoT devices remotely while maintaining security and privacy.
Benefits of IoT VPC Integration
Integrating IoT devices into a VPC offers several advantages, including enhanced security, scalability, and centralized management. By isolating IoT devices in a private network, organizations can prevent unauthorized access and ensure data integrity. Additionally, VPCs provide the flexibility to scale resources as needed, making them ideal for IoT deployments.
Raspberry Pi in IoT Deployments
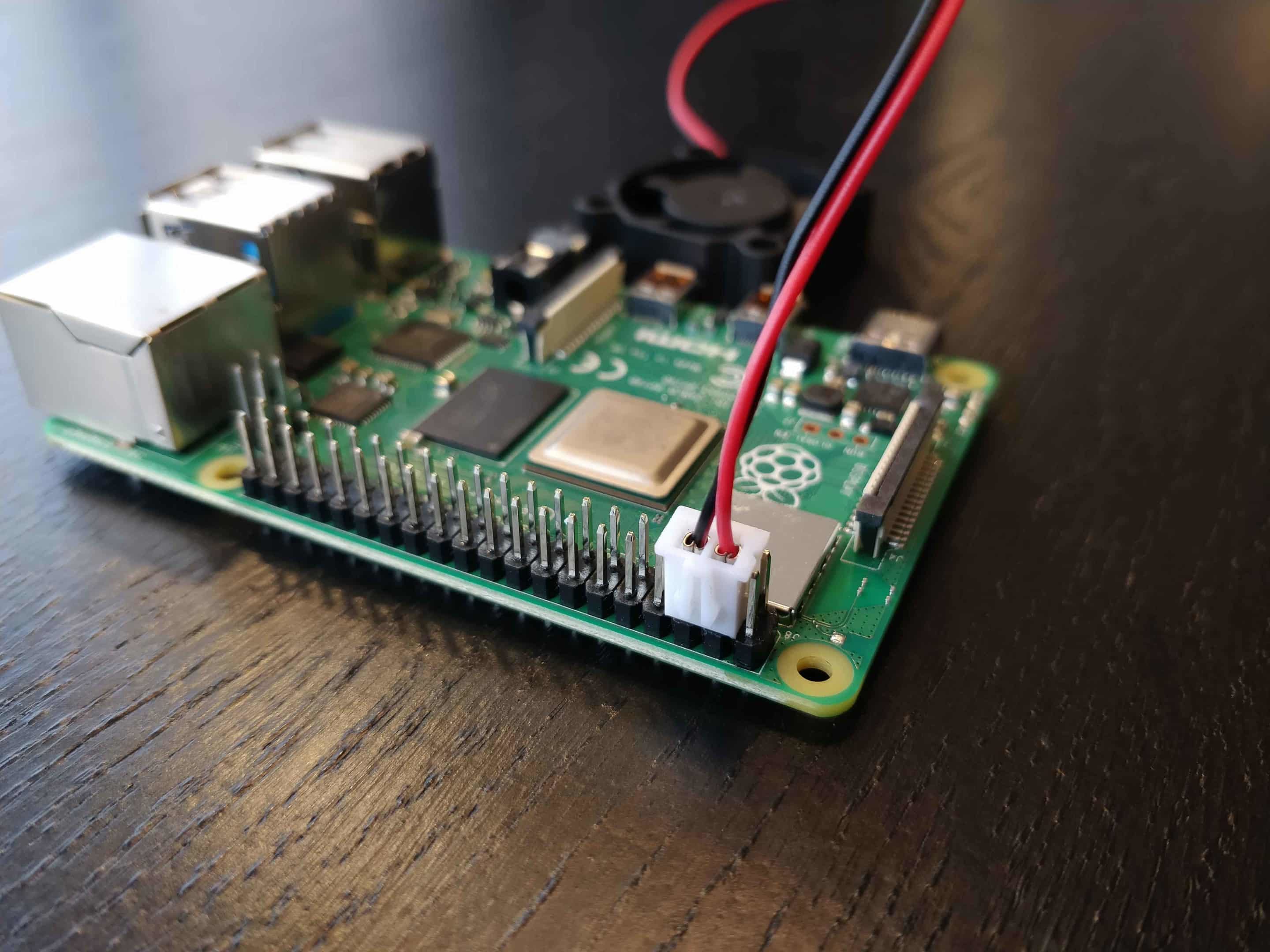
The Raspberry Pi is a popular single-board computer widely used in IoT projects due to its affordability, versatility, and ease of use. It serves as an excellent platform for developing and deploying IoT applications, from home automation to industrial monitoring systems.
Key Features of Raspberry Pi
- Compact and lightweight design
- Support for multiple operating systems
- Built-in connectivity options (Wi-Fi, Bluetooth)
- Extensive community support and resources
Why Secure Connections Are Critical
IoT devices are vulnerable to cyberattacks, making secure connections essential for protecting sensitive data and ensuring system integrity. Unauthorized access to IoT devices can lead to data breaches, financial losses, and reputational damage. Implementing robust security measures, such as encryption and authentication, is crucial for safeguarding IoT ecosystems.
Common IoT Security Threats
- Denial-of-Service (DoS) attacks
- Data interception and tampering
- Firmware vulnerabilities
- Unauthorized device access
Setting Up a VPC for IoT Devices
Setting up a VPC involves configuring network settings, creating subnets, and defining security groups. This process ensures that IoT devices operate within a secure and isolated environment, reducing the risk of external threats.
Steps to Configure a VPC
- Choose a cloud provider offering VPC services (e.g., AWS, Google Cloud, Azure).
- Create a VPC with appropriate CIDR block settings.
- Set up subnets for public and private access.
- Configure routing tables and internet gateways.
Securing Remote IoT Connections
Securing remote IoT connections involves implementing encryption, authentication, and authorization mechanisms. These measures ensure that only authorized devices and users can access the VPC and its resources.
Read also:Engaging Insights On The Talented Dafne Keens Education And Career
Encryption Techniques
Encryption is a fundamental aspect of IoT security, protecting data during transmission and storage. Common encryption protocols used in IoT include:
- TLS/SSL for secure communication
- AES for data encryption
- SSH for secure remote access
Tools and Technologies for Secure IoT
Several tools and technologies can enhance the security of IoT VPC deployments. These include firewalls, intrusion detection systems (IDS), and security information and event management (SIEM) solutions.
Recommended Tools
- Firewalla for network security
- Snort for intrusion detection
- Splunk for SIEM capabilities
Best Practices for IoT Security
Adopting best practices for IoT security is essential for maintaining a secure and resilient infrastructure. These practices include regular firmware updates, strong password policies, and network segmentation.
Implementing Best Practices
- Regularly update device firmware and software
- Enforce strong authentication mechanisms
- Segment networks to isolate critical devices
Cost-Effective Solutions for IoT VPC
Implementing secure IoT VPC solutions doesn't have to be expensive. By leveraging open-source tools and free cloud services, organizations can achieve secure IoT deployments without significant financial investment.
Free Resources for IoT Security
- OpenVPN for secure tunneling
- Let's Encrypt for free SSL certificates
- Fail2Ban for intrusion prevention
Troubleshooting Common Issues
When setting up a secure IoT VPC connection, you may encounter various challenges, such as connectivity issues or configuration errors. Troubleshooting these problems requires a systematic approach and familiarity with the tools and technologies involved.
Common Troubleshooting Steps
- Verify network settings and configurations
- Check firewall and security group rules
- Test device connectivity using ping and traceroute
Conclusion
Securing remote IoT VPC connections is a critical aspect of modern digital infrastructure. By following the guidelines and best practices outlined in this article, you can ensure that your Raspberry Pi-based IoT deployments remain safe and secure. Remember to regularly update your devices, implement strong authentication mechanisms, and leverage cost-effective tools and technologies to achieve a secure IoT ecosystem.
We encourage you to share your thoughts and experiences in the comments section below. Additionally, feel free to explore other articles on our site for more insights into IoT and cloud computing. Together, let's build a safer and more connected world.