In today's interconnected world, SSH (Secure Shell) has emerged as one of the most secure and reliable ways to remotely manage IoT devices. Whether you're a beginner or a seasoned professional, understanding SSH RemoteIoT is crucial for ensuring seamless communication and security in your IoT infrastructure. This tutorial will guide you through the fundamentals and advanced aspects of SSH RemoteIoT, empowering you to leverage its full potential.
SSH RemoteIoT has become an essential tool for developers, IT professionals, and hobbyists alike. It allows you to securely connect to and control IoT devices from anywhere in the world, ensuring that your systems remain safe and operational. By mastering SSH RemoteIoT, you can significantly enhance the efficiency of your IoT projects and minimize potential risks.
In this comprehensive guide, we'll explore everything you need to know about SSH RemoteIoT. From setting up your environment to troubleshooting common issues, this tutorial aims to provide you with the knowledge and tools necessary to confidently implement SSH in your IoT projects. Let's dive in!
Read also:Whats On Disney The Ultimate Guide To Streaming Magic
Table of Contents
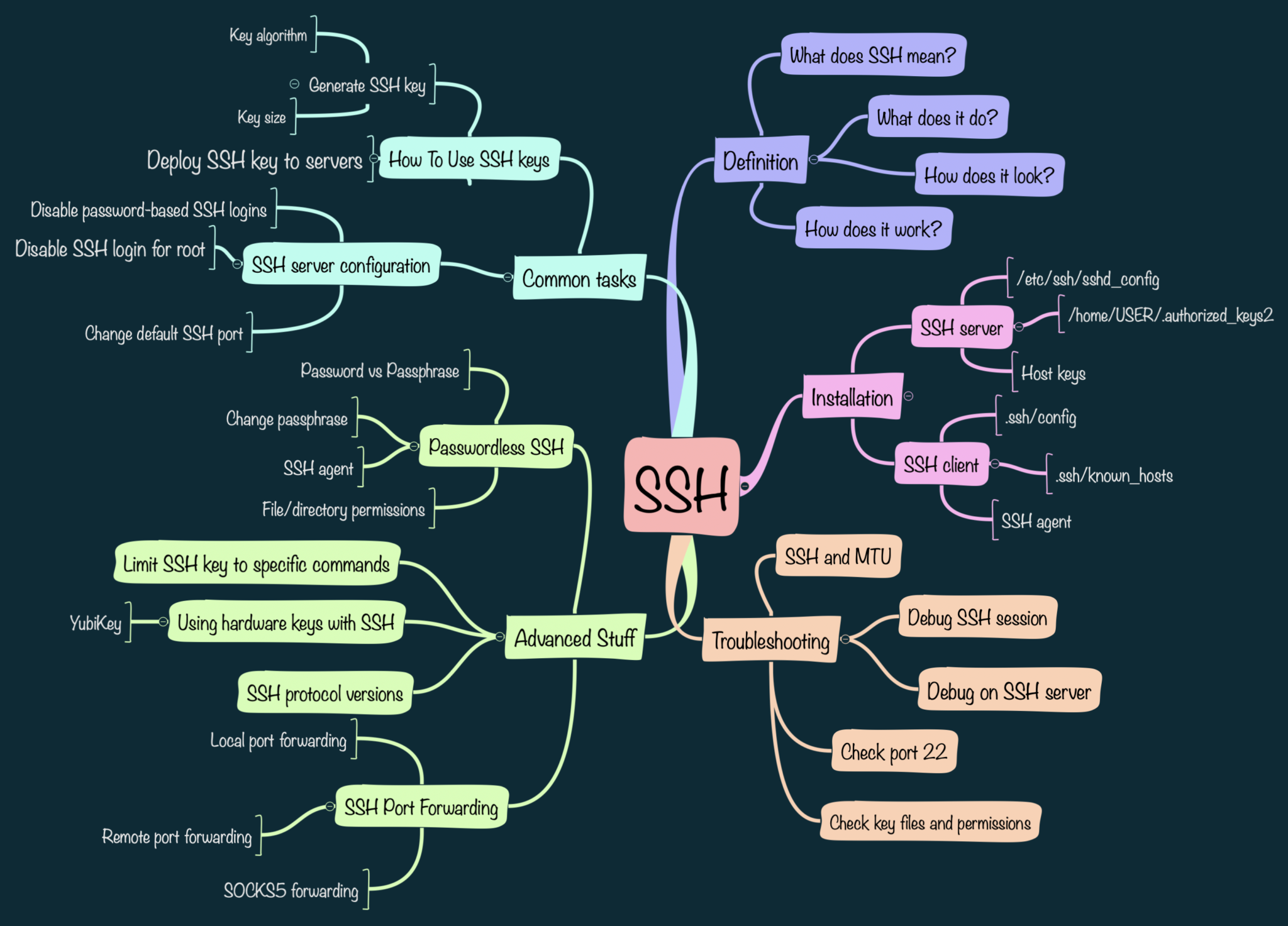
- Introduction to SSH RemoteIoT
- Benefits of Using SSH for RemoteIoT
- Setting Up SSH for RemoteIoT
- SSH Security Best Practices
- Essential SSH Commands for RemoteIoT
- Automating SSH Connections for IoT Devices
- Troubleshooting Common SSH Issues
- Tools and Software for SSH RemoteIoT
- Real-World Examples of SSH in IoT
- The Future of SSH in RemoteIoT
Introduction to SSH RemoteIoT
SSH, or Secure Shell, is a network protocol designed to securely connect to remote devices. When it comes to IoT (Internet of Things), SSH plays a pivotal role in enabling remote access and management of devices. In this section, we'll explore the basics of SSH RemoteIoT and its significance in modern IoT ecosystems.
Why SSH is Essential for IoT
IoT devices often operate in environments where physical access is limited or impossible. SSH provides a secure and encrypted channel for remote communication, ensuring that your devices remain accessible and manageable from anywhere. This is particularly important for industries such as manufacturing, healthcare, and agriculture, where IoT devices are deployed in remote locations.
Key Features of SSH RemoteIoT
- Encrypted communication to protect sensitive data.
- Authentication mechanisms to ensure only authorized users can access devices.
- Support for various commands and scripts to automate tasks.
- Compatibility with a wide range of IoT devices and platforms.
Benefits of Using SSH for RemoteIoT
Implementing SSH for RemoteIoT offers numerous advantages that make it an indispensable tool for IoT projects. In this section, we'll delve into the key benefits of using SSH in your IoT infrastructure.
Enhanced Security
SSH provides robust encryption and authentication mechanisms, ensuring that your IoT devices are protected from unauthorized access and cyber threats. By leveraging SSH, you can significantly reduce the risk of data breaches and ensure the integrity of your IoT systems.
Scalability
SSH is highly scalable and can be used to manage thousands of IoT devices simultaneously. This makes it ideal for large-scale IoT deployments where multiple devices need to be monitored and controlled remotely.
Setting Up SSH for RemoteIoT
Setting up SSH for RemoteIoT requires careful planning and configuration. In this section, we'll walk you through the steps to configure SSH on your IoT devices and establish secure connections.
Read also:Best Stocks To Buy Now Why 5starsstockscom To Buy Is Your Ultimate Guide
Step 1: Install SSH on Your Device
Before you can use SSH, you need to install an SSH server on your IoT device. Most modern IoT platforms, such as Raspberry Pi and Arduino, come with SSH pre-installed. If not, you can install it using package managers like apt or yum.
Step 2: Configure SSH Settings
Once SSH is installed, you need to configure its settings to ensure secure and reliable connections. This includes setting up user accounts, enabling public key authentication, and disabling password-based authentication for added security.
SSH Security Best Practices
Security is paramount when it comes to SSH RemoteIoT. In this section, we'll discuss best practices to secure your SSH connections and protect your IoT devices from potential threats.
Use Strong Passwords
While public key authentication is recommended, if you must use passwords, ensure they are strong and unique. Avoid using default passwords or easily guessable combinations.
Enable Two-Factor Authentication
Two-factor authentication adds an extra layer of security to your SSH connections. By requiring a second form of verification, such as a one-time code, you can significantly reduce the risk of unauthorized access.
Essential SSH Commands for RemoteIoT
Mastering SSH commands is essential for effectively managing your IoT devices. In this section, we'll cover some of the most commonly used SSH commands for RemoteIoT.
Connecting to a Remote Device
To connect to a remote IoT device using SSH, you can use the following command:
ssh username@device_ip_address
Transferring Files
SSH also allows you to securely transfer files between your local machine and remote IoT devices. You can use the SCP (Secure Copy) command for this purpose:
scp local_file_path username@device_ip_address:remote_file_path
Automating SSH Connections for IoT Devices
Automating SSH connections can save you time and effort, especially when managing multiple IoT devices. In this section, we'll explore tools and techniques for automating SSH in your IoT projects.
Using SSH Keys for Automation
SSH keys provide a secure and convenient way to automate connections to IoT devices. By generating a public-private key pair and configuring your devices to accept the public key, you can establish passwordless connections.
Scheduling Tasks with Cron
You can use cron jobs to schedule regular tasks on your IoT devices via SSH. This is particularly useful for tasks such as data collection, system monitoring, and software updates.
Troubleshooting Common SSH Issues
Even with proper configuration, SSH connections can sometimes encounter issues. In this section, we'll discuss common problems and how to resolve them.
Connection Refused
If you're unable to connect to your IoT device via SSH, ensure that the SSH service is running and that the device's firewall allows incoming connections on port 22.
Authentication Failed
Authentication failures can occur due to incorrect credentials or misconfigured SSH settings. Double-check your username, password, and key files to resolve this issue.
Tools and Software for SSH RemoteIoT
Several tools and software can enhance your SSH RemoteIoT experience. In this section, we'll introduce some of the most popular options.
Putty
Putty is a widely used SSH client for Windows users. It provides a simple interface for connecting to remote IoT devices and supports various authentication methods.
SSHFS
SSHFS allows you to mount remote file systems over SSH, enabling seamless access to files on your IoT devices from your local machine.
Real-World Examples of SSH in IoT
SSH is used in a variety of real-world IoT applications. In this section, we'll explore some examples to illustrate its versatility and effectiveness.
Smart Home Automation
SSH enables remote management of smart home devices, allowing users to control lighting, thermostats, and security systems from anywhere in the world.
Industrial IoT
In industrial settings, SSH is used to monitor and control machinery and equipment, ensuring optimal performance and minimizing downtime.
The Future of SSH in RemoteIoT
As IoT continues to evolve, SSH will remain a critical component of remote management solutions. In this section, we'll discuss emerging trends and future developments in SSH RemoteIoT.
Quantum-Safe Cryptography
With the advent of quantum computing, there is growing interest in developing quantum-safe cryptographic algorithms for SSH. These algorithms will ensure the security of IoT devices even in the face of advanced cyber threats.
Integration with AI
AI-driven tools are being developed to enhance SSH functionality, enabling smarter automation and more efficient management of IoT devices.
Conclusion
In conclusion, SSH RemoteIoT is a powerful tool that offers numerous benefits for managing IoT devices. By following the guidelines and best practices outlined in this tutorial, you can ensure secure and reliable connections to your IoT infrastructure. We encourage you to explore the various tools and techniques discussed here and apply them to your projects.
Feel free to leave a comment below if you have any questions or suggestions. Don't forget to share this article with others who might find it useful. For more in-depth guides and tutorials, explore our other articles on IoT and related technologies.