In today's digital age, the best SSH RemoteIoT solutions play a crucial role in ensuring secure communication between devices and networks. With the rapid growth of IoT devices, businesses and individuals are increasingly relying on SSH (Secure Shell) for managing remote systems securely. This article dives deep into the world of SSH RemoteIoT, exploring its benefits, applications, and the most reliable tools available to enhance your remote access experience.
SSH RemoteIoT is not just a buzzword; it represents the intersection of secure communication protocols and the Internet of Things (IoT). By leveraging SSH, users can establish encrypted connections to control and manage IoT devices remotely, protecting sensitive data and operations from unauthorized access.
This article aims to provide comprehensive insights into the best SSH RemoteIoT solutions available, helping you make informed decisions to secure your IoT infrastructure. Whether you're a tech enthusiast or a business professional, understanding SSH and its applications in IoT is essential for maintaining robust cybersecurity practices.
Read also:Discover The World Of Ssbbw Adeline A Comprehensive Guide To Curvy Confidence And Empowerment
Table of Contents
- Introduction to SSH RemoteIoT
- Why SSH is the Best Option for RemoteIoT
- Top SSH Tools for RemoteIoT Management
- Security Benefits of Using SSH in RemoteIoT
- Implementation Steps for SSH RemoteIoT
- Troubleshooting Common SSH RemoteIoT Issues
- Best Practices for SSH RemoteIoT
- Comparison of SSH RemoteIoT Solutions
- Future Trends in SSH RemoteIoT
- Conclusion
Introduction to SSH RemoteIoT
Understanding SSH and Its Role in IoT
SSH, or Secure Shell, is a cryptographic network protocol designed for secure communication over unsecured networks. It is widely used for remote command-line login and data transfer. In the context of IoT, SSH RemoteIoT ensures that devices can be managed securely, even when accessed from remote locations.
The best SSH RemoteIoT solutions offer robust encryption, authentication mechanisms, and reliable performance, making them indispensable for modern IoT ecosystems. By encrypting all data transmitted between devices and servers, SSH minimizes the risk of data breaches and unauthorized access.
Key Features of SSH RemoteIoT
- End-to-end encryption for secure data transmission.
- Strong authentication methods, including public-key cryptography.
- Support for various IoT devices and operating systems.
- Scalability to accommodate growing IoT networks.
Why SSH is the Best Option for RemoteIoT
When it comes to securing IoT devices, SSH stands out as the best option for remote access. Unlike other protocols, SSH provides a secure channel for communication, protecting sensitive data and operations from cyber threats.
According to a report by Statista, the global IoT market is projected to reach $1.5 trillion by 2030, highlighting the increasing reliance on IoT technologies. With this growth comes the need for secure solutions like SSH RemoteIoT to safeguard IoT infrastructure.
Advantages of SSH RemoteIoT
- High-level encryption ensures data integrity and confidentiality.
- Supports secure file transfer using SFTP (SSH File Transfer Protocol).
- Compatible with a wide range of IoT devices and platforms.
- Reduces the risk of cyberattacks and unauthorized access.
Top SSH Tools for RemoteIoT Management
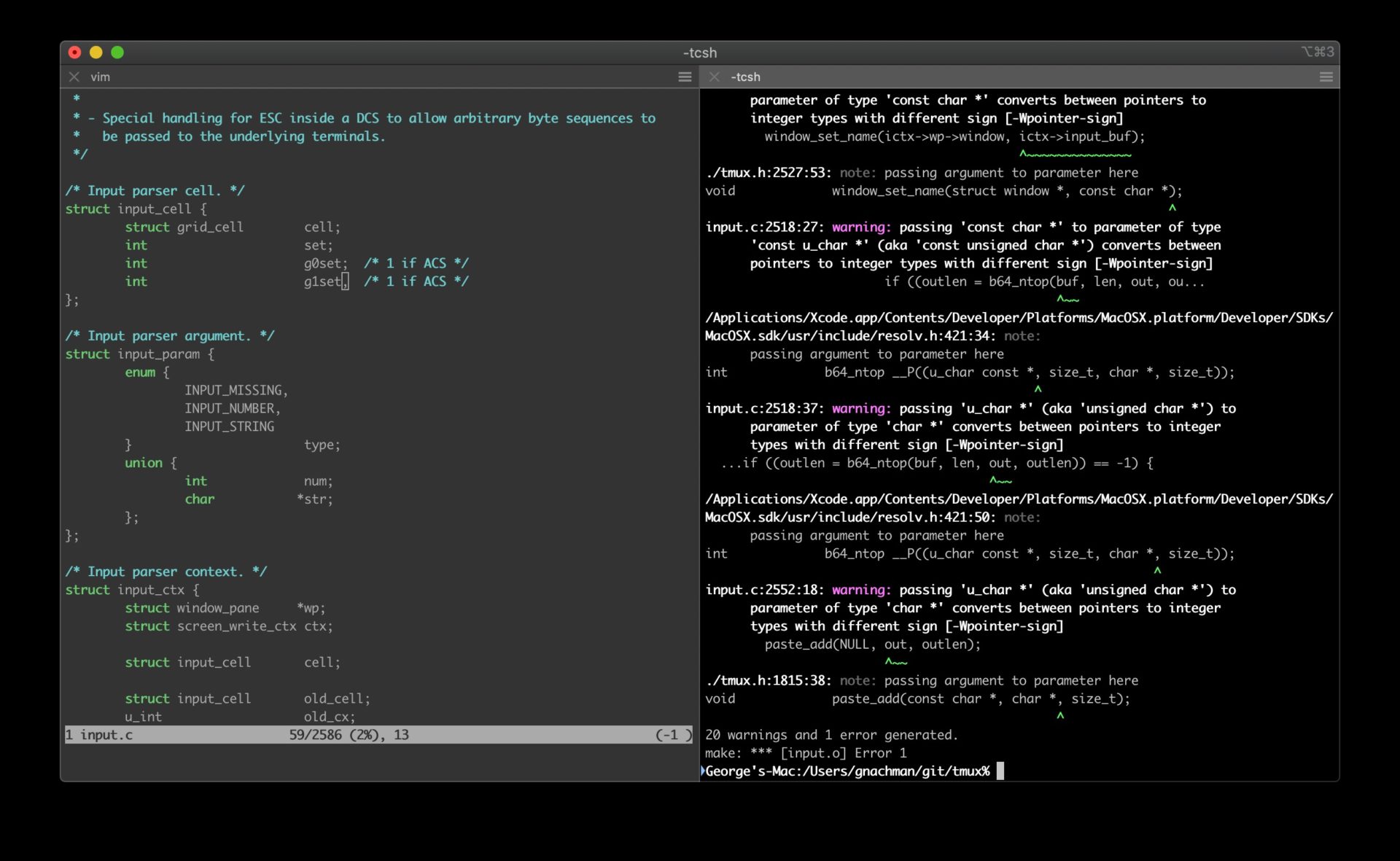
1. OpenSSH
OpenSSH is one of the most popular SSH tools, widely used for managing remote systems. It is open-source, highly customizable, and supports a variety of operating systems, making it an ideal choice for IoT environments.
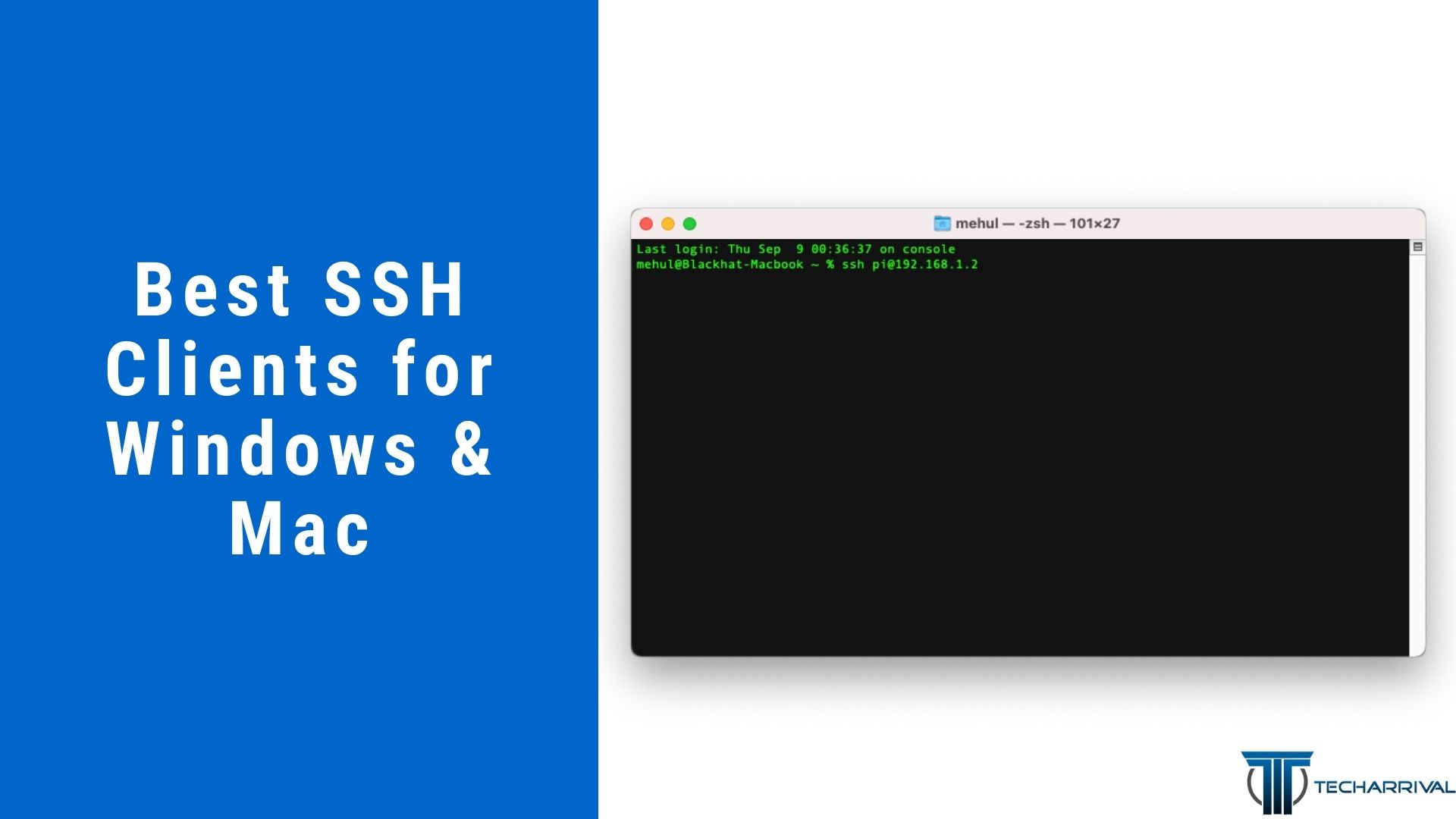
2. PuTTY
PuTTY is a free SSH client for Windows and Unix platforms, offering a user-friendly interface for remote access. Its lightweight design and extensive feature set make it a preferred tool for SSH RemoteIoT management.
Read also:Spongebob Grandma Unveiling The Iconic Character And Her Role In Bikini Bottom
3. Bitvise SSH Client
Bitvise SSH Client provides advanced security features, including two-factor authentication and tunneling capabilities. It is particularly useful for managing IoT devices in enterprise environments.
Security Benefits of Using SSH in RemoteIoT
Implementing SSH in your RemoteIoT infrastructure offers numerous security benefits, protecting your devices and data from potential threats. Here are some key advantages:
- Encryption of all communication between devices and servers.
- Strong authentication mechanisms to verify user identities.
- Protection against man-in-the-middle (MITM) attacks.
- Secure file transfer using SFTP, reducing the risk of data leaks.
Implementation Steps for SSH RemoteIoT
Step 1: Install SSH Client and Server
Begin by installing an SSH client on your local machine and an SSH server on your IoT devices. Popular SSH clients like PuTTY and OpenSSH are widely available and easy to set up.
Step 2: Configure Authentication Methods
Set up secure authentication methods, such as public-key cryptography, to ensure only authorized users can access your IoT devices. Avoid using weak passwords or default credentials.
Step 3: Test the Connection
Once the SSH server is configured, test the connection to ensure secure communication between your local machine and IoT devices. Verify that data is encrypted during transmission.
Troubleshooting Common SSH RemoteIoT Issues
Even with the best SSH RemoteIoT solutions, issues may arise during implementation. Here are some common problems and their solutions:
- Connection Refused: Ensure the SSH server is running and the correct port is open.
- Authentication Failed: Double-check your credentials and authentication settings.
- Slow Performance: Optimize your network configuration and reduce unnecessary data transfers.
Best Practices for SSH RemoteIoT
To maximize the security and performance of your SSH RemoteIoT setup, follow these best practices:
- Regularly update SSH clients and servers to patch security vulnerabilities.
- Use strong, unique passwords or public-key authentication for secure access.
- Limit access to authorized users and monitor activity logs for suspicious behavior.
- Implement firewall rules to restrict access to SSH ports from untrusted sources.
Comparison of SSH RemoteIoT Solutions
OpenSSH vs. PuTTY vs. Bitvise
Choosing the right SSH tool depends on your specific needs and preferences. Below is a comparison of three popular SSH RemoteIoT solutions:
- OpenSSH: Open-source, highly customizable, and widely supported across platforms.
- PuTTY: User-friendly interface, lightweight, and ideal for Windows users.
- Bitvise: Advanced security features, suitable for enterprise environments.
Future Trends in SSH RemoteIoT
As the IoT landscape continues to evolve, SSH RemoteIoT solutions are expected to become more advanced and user-friendly. Key trends to watch include:
- Integration with AI and machine learning for enhanced security analytics.
- Development of quantum-resistant encryption algorithms to future-proof SSH protocols.
- Increased adoption of cloud-based SSH solutions for scalable IoT management.
Conclusion
SSH RemoteIoT is a powerful tool for securing IoT devices and networks, offering robust encryption, authentication, and performance features. By selecting the best SSH RemoteIoT solutions and following best practices, you can protect your IoT infrastructure from cyber threats and ensure seamless remote access.
We encourage you to share your thoughts and experiences with SSH RemoteIoT in the comments section below. For more information on cybersecurity and IoT technologies, explore our other articles and resources. Together, let's build a safer and more connected digital world!
Data Sources:
- Statista - Global IoT Market Report
- OpenSSH Official Documentation
- PuTTY User Manual
- Bitvise SSH Client Documentation